Hoxhunt and RansomLeak both reject the idea that security training should be a passive, video-heavy compliance exercise. Both platforms bet on engagement over lecture slides. But they solve the engagement problem in fundamentally different ways.
Hoxhunt builds AI-adaptive phishing simulations that adjust difficulty based on each employee’s performance. The system learns who falls for what and sends progressively harder attacks to keep people challenged. It is a sophisticated approach to the phishing simulation problem specifically.
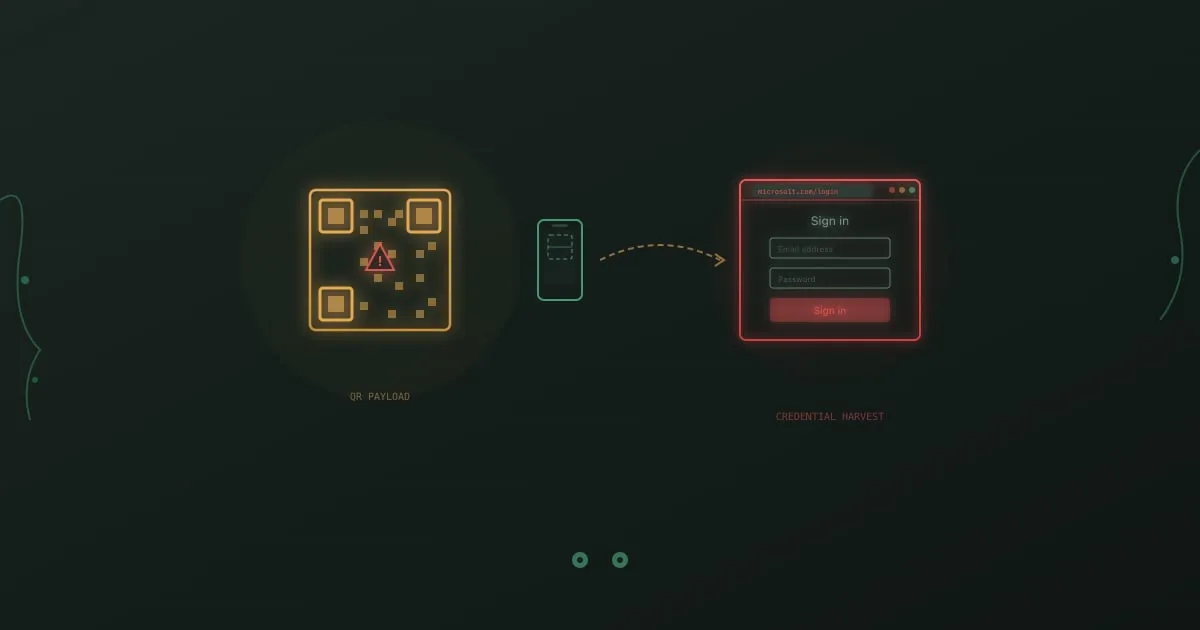
RansomLeak builds interactive 3D simulations where employees practice handling full attack scenarios. Not just phishing, but ransomware, social engineering, vishing, deepfakes, AI security threats, and GDPR compliance. The focus is hands-on practice across the full spectrum of security risks.
Both approaches work. The question is which one matches what your organization actually needs.